I found this interesting: https://github.com/spaceraccoon/vulnerability-spoiler-alert
Reasons:
It’s not easy to fix the vulnerabilities in open source projects like bitcoin core.
https://xcancel.com/fanquake/status/1977396233237864530
https://xcancel.com/christine_dkim/status/1978121490336796945
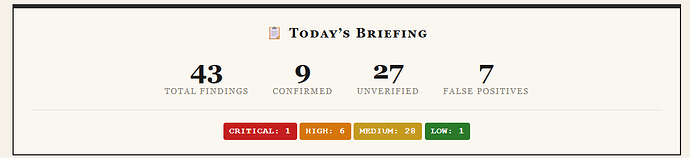
The results in this experiment look good enough based on some of the repositories it scans everyday.
opened 02:59PM - 16 Feb 26 UTC
vulnerability
true-positive
severity:high
## Potential Security Vulnerability Detected
**Repository:** [nodejs/node](http… s://github.com/nodejs/node)
**Commit:** [4d867af](https://github.com/nodejs/node/commit/4d867af6c5d4b47b240ae4050265eb806f36e61e)
**Author:** Shelley Vohr
**Date:** 2026-02-16T14:59:14Z
### Commit Message
```
build: generate_config_gypi.py generates valid JSON
PR-URL: https://github.com/nodejs/node/pull/61791
Reviewed-By: Chengzhong Wu <legendecas@gmail.com>
Reviewed-By: Colin Ihrig <cjihrig@gmail.com>
Reviewed-By: Luigi Pinca <luigipinca@gmail.com>
```
### Pull Request
**PR:** [#61791 - build: `generate_config_gypi.py` generates valid JSON](https://github.com/nodejs/node/pull/61791)
**Labels:** tools, author ready
**Description:**
Refs https://github.com/nodejs/node/pull/60794
`generate_config_gypi.py` needs to generate valid JSON and didn't.
<!--
Before submitting a pull request, please read:
- the CONTRIBUTING guide at https://github.com/nodejs/node/blob/HEAD/CONTRIBUTING.md
- the commit message formatting guidelines at
https://github.com/nodejs/node/blob/HEAD/doc/contributing/pull-requests.md#commit-message-guidelines
For code changes:
1. Include tests for any bug fixes or new features.
2. Update docum...
### Analysis
**Vulnerability Type:** Code Injection
**Severity:** High
### Description
The code used eval() to parse configuration data, which allows arbitrary Python code execution if an attacker can control the node_builtin_shareable_builtins configuration value. The patch replaces eval() with json.loads() to safely parse JSON data.
### Affected Code
```
eval(config['node_builtin_shareable_builtins'])
```
### Proof of Concept
```
An attacker could set node_builtin_shareable_builtins to '__import__("os").system("rm -rf /")' which would execute arbitrary shell commands when eval() processes it during the build configuration generation.
```
---
*This issue was automatically created by [Vulnerability Spoiler Alert](https://github.com/spaceraccoon/vulnerability-spoiler-alert-action).*
*Detected at: 2026-02-16T14:59:50.675Z*
Questions:
How would this affect bitcoin core and other open source bitcoin projects?
Has there ever been an incident in bitcoin core where a vulnerability was exploited before a release because it was easy to spot the fix in the commits?
Note: Such reviews can also be used to find bugs in the commits and not just the bug fix.
Archive